
Researchers at the Palo Alto Networks American security company they have discovered in 132 applications for Android Windows malware, although this circumstance would not have any effect on the operating system itself.
According to the results of this study, the malware came in the form of “small, hidden IFrames” or HTML documents embedded in other HTML documents that were linking to malicious insider domains of applications.
132 applications infected with a similar origin
Although 132 applications affected are the work of a total of seven developers that are not related to each other, Palo Alto Networks says that all seem to be originating in Indonesia and that were probably not aware of the existence of the malware.
“Our research indicates that these infected application developers are not to blame, but they are the victims,” the researchers said. “We believe that it is more likely that developers of applications development platforms were infected with malware that looks for HTML pages and injects malicious content at the end of the HTML pages that is.”
Infected by this malware applications are very varied, from recipe apps until some other design or gardening but all have as common denominator that employ the same technology to display the static HTML pages:
All applications have in common is that they use Android WebView to display static HTML pages. At first glance, each page does nothing more than load images stored locally, and show encoded text. However, an in-depth analysis of the actual HTML code reveals a small hidden IFrame linking with well known malicious domains. Although the linked domains were reduced at the time of the research, the fact that many Google Play applications are infected is remarkable.
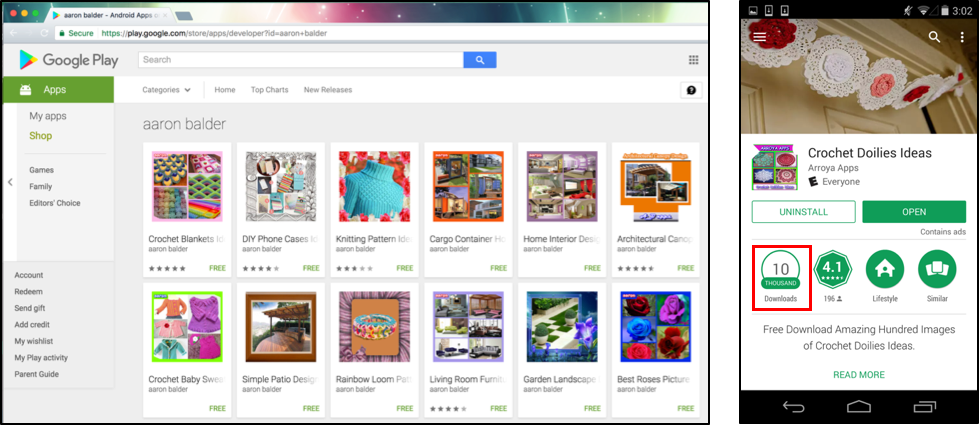
One of the applications that is infected with this malware | Image: Palo Alto Networks
In this case, the detected malware has not caused any damage, basically because the file that is run is designed for Windows and not for Android:
What is more remarkable is that one of the pages also infected attempts to download and install a Microsoft Windows malicious executable file at the time of loading the page, but as the device is not running Windows, it will not run. This behavior fits the category of threats not Android recently launched by Google Android Security. According to the classification, the non-Android threat refers to applications that may not cause harm to the user or the Android device, but contains potentially harmful to other platform components.
However, Palo Alto Networks warns that this could lead to a worrisome scenario in which the platforms are used as carriers of malware that operates in other places:
Currently, infected applications will not cause damage to Android users. However, this represents a novel way that the platforms will be a “carrier” of malware: not infected, but that they spread the malware to other platforms without realizing it. Similar to the attack XcodeGhost that we identified in 2015, this threat shows how attackers developers can impact end users.
The security company has also pointed out that, with some settings, attackers could use this kind of malware to “Modify the internal logic of the application, i.e. Add utilities of routing, additional permissions or let malicious APK files to increase their capabilities”.
Palo Alto that has announced its discovery and the results of its investigation to the Google security team, and that infected applications have already been removed from the Google Play Store.
We have reported our findings to the Google security team and all infected applications have been removed from Google Play.
You think that the system that has Google to find malware running in the best possible way, especially considering the existence of hundreds of millions of Android devices and millions of applications or, conversely, estimate that their efforts may be higher?



